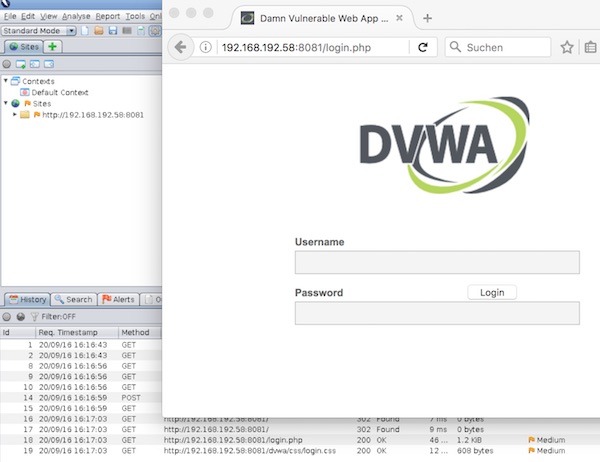
Pappy Proxy (Proxy Attack Proxy ProxY) is an open source intercepting proxy for performing web application security tests. It is similar to BurpSuite, ZAP and so on. The benefit is the command line!
Installation
# update system
$ yum update -y
# install epel
$ yum -y install epel-release
# install needed packages
$ yum install -y git python-pip python-devel gcc libffi-devel libxml2 libxml2-devel libxslt libxslt-devel openssl-devel
# clone repository
$ git clone --recursive https://github.com/roglew/pappy-proxy.git
# change directory
$ cd pappy-proxy/
# install pappy-proxy
$ pip install .
# run help
$ pappy --help
# start up in lite mode
$ pappy -lSo pappy is started … we can configure and test it (via lite-mode).
# generate certificates
pappy> gencerts
# test proxy from other terminal
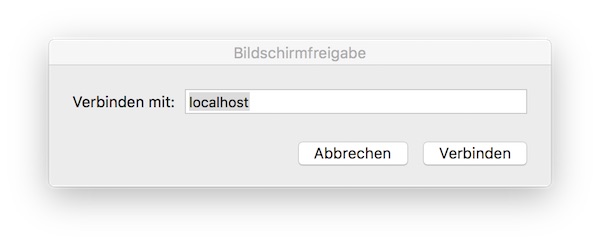
$ curl -x http://localhost:8000 -L http://google.com
# list requests
pappy> ls
# prints the full response to a request
pappy> vfs <id>
# exit pappy-proxy lite mode
pappy> quitPrepare a project
# create project directory
$ mkdir myProject
# change directory
$ cd myProjectWe need to start pappy shortly to create config.json file.
# start pappy-proxy
$ pappy
# exit pappy-proxy
pappy> quit
# show directory content
$ ls -la
# modify settings
$ vim config.json
# start up pappy-proxy
$ pappy
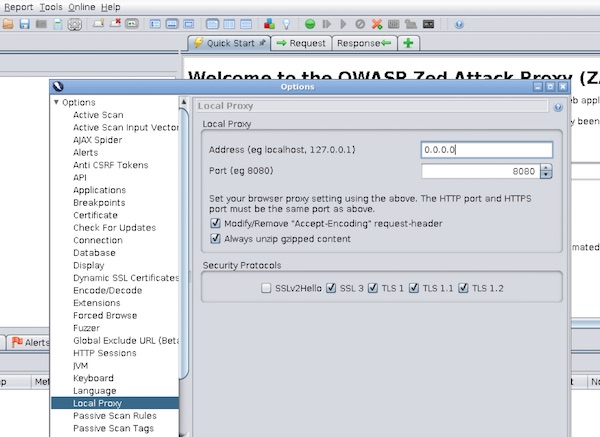
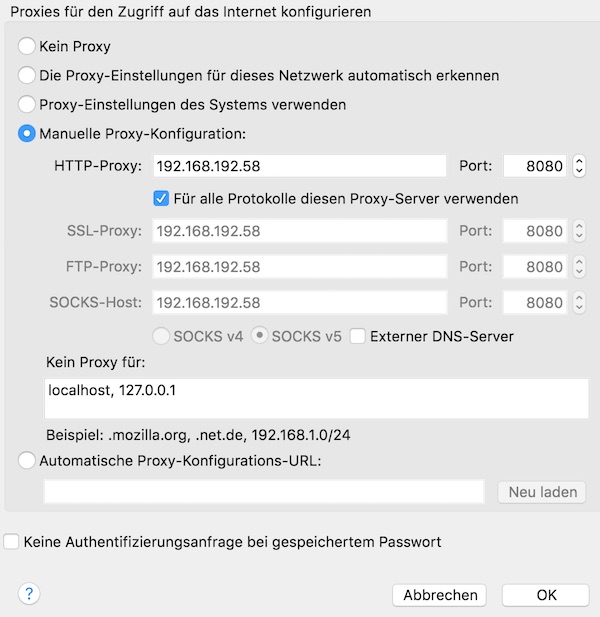
...Note: By default the proxy is running on port 8000 – bound to localhost. You need to modify the config.json. For more information read the docs.