This time I am not writing a tutorial on software. I would like to introduce you to my DIY project here. At a later point in time, however, I will focus on the newly used and partly self-developed software deeper.
Why this little project?
Over the years I have accumulated various electronic devices, cables and lots of other electrical scrap. Always storing it neatly is hell (I hate cardboard or plastic boxes). In addition, I do not live alone and should actually take all other people in the household into account. So I was looking for a better solution for my beloved girlfriend, my dog (who also likes to eat things) and of course my self. In addition, everything should be tidy, ready to hand and mobile. When I then remembered my training as an electrician (especially on my toolbox), it quickly became clear to me which solution would be suitable for me. Different Suitcases made of aluminum (light and stable), where each of them have slightly different scope.

What’s in there?
Actually there are several suitcases with different contents (depending on what I have planned). I would like to show you now, two of my personal favorites here.
Suitcase 1
This called by myself the RadioBox.

- Raspberry Pi 4 Model B/8GB
- Yardstick One (incl. ANT700 antenna)
- Ubertooth One (incl. 2.4 GHz antenna)
- ALFA Atheros (AWUS036NHA)
- BashBunny + RubberDucky
- GL.iNet GL-AR300M (Shadow) Mini VPN Router
- Fresh’n’Rebel Powerbank (18000 mAh)
- external USB SSD
- HackRF One (incl. ANT500)
- Waveshare monitor FHD (12.5inch, 1920×1080 pixels, IPS screen)
Suitcase 2
This called by myself the Hak5Box

- Raspberry Pi 4 Model B/8GB
- Keysy + SharkJack + KeyLogger
- OM.G Cabel’s + Cable Programmer + Malicious cable detector
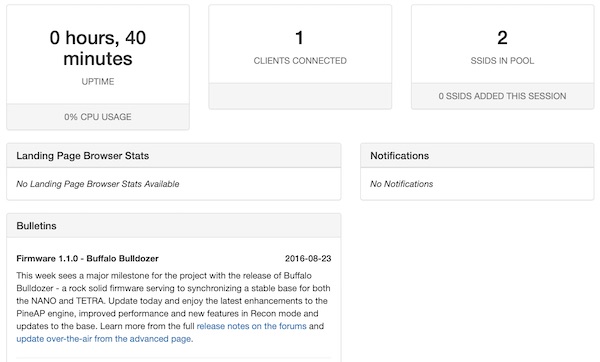
- WiFi Pineapple (M7)
- Alfa Network APA-M04 7dBi WLAN antenna (2,4 GHz)
- Fresh’n’Rebel Powerbank (18000 mAh)
- Waveshare monitor FHD (12.5inch, 1920×1080 pixels, IPS screen)
In addition, all cases are filled with brackets and foam so that the connecting cables are not visible (this is not shown in the pictures) and each device has a specific place.
Do you want such suitcases, too?
If you also want one (or more) suitcases and don’t have the time or inclination to build them yourself – just contact me! We can talk about it.
Note: It is important to know that each case and its contents are freely configurable (but it should fit).